How to check a USDT transaction
Learn how to verify a USDT transaction using blockchain explorers, KYT services and analytics platforms to ensure cryptocurrency transfers are secure.
ReadWith us, your work in the digital space is predictable and secure
An experienced team, powerful tools and technologies, high ethical standards

Crypto security of digital assets
End-to-end data analytics
Cybersecurity for business and life
We will quickly take on your request and review it thoroughly.
We will look into your request in detail and offer an optimal plan of action. We will provide a list of additional services to solve any related problems as necessary.
Our experts work in accordance with an approved plan until the desired goals are achieved in full.
Comprehensive security of business processes and private assets to help you avoid too costly mistakes

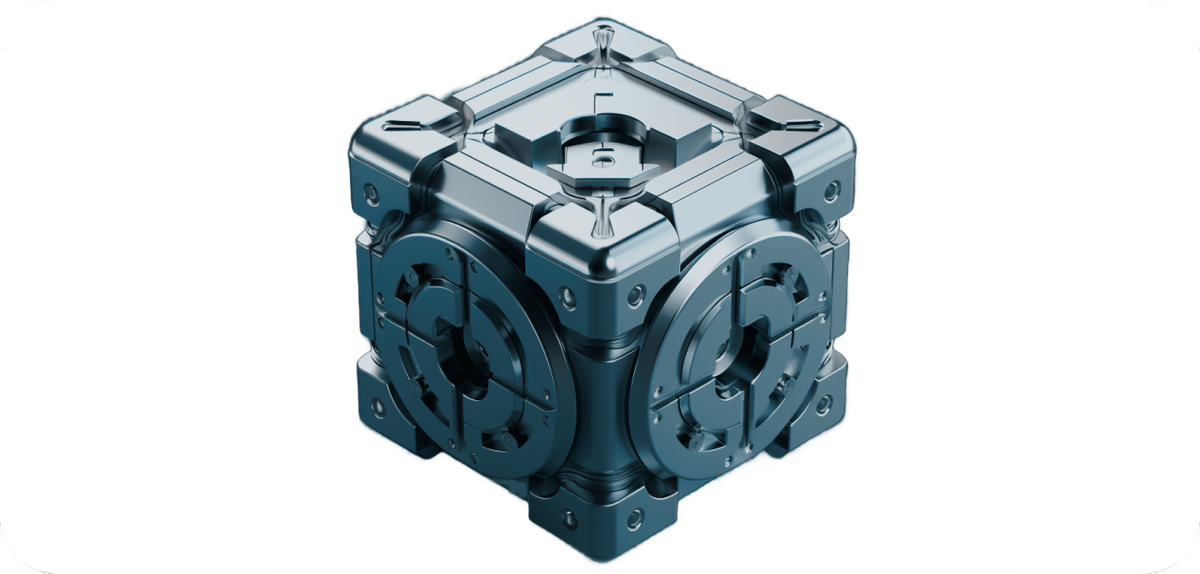

Comprehensive security solutions are key to the best possible control over your resources.
Complete the form to get advice. Make sure you and your business have a reliable protection against any cyber threats.
Наш менеджер свяжется с вами в течение рабочего дня.